Collapsing the Tech Stack: Why BYO/Self-Service IT is Your Best Starting Point
Streamlining your BYO stack is a smart proof of concept for enhancing security, productivity, and user experience, while cutting costs.

The complexity of enterprise tech stacks has surged significantly within the past decade. This partially stems from the growing need to manage and secure an expanding array of devices and applications.
The idea of collapsing the tech stack — streamlining and simplifying the tools and platforms your organization uses — is not just a trend; it's a strategic imperative. Progressive CIOs and IT leaders are dramatically condensing their tech stack with a single tool: the Enterprise Browser. This approach can significantly enhance security, boost productivity, improve the end-user experience, and reduce recurring costs.
But how do you start this journey, and what are the critical considerations? Before we dive into this, it’s important to understand how we got here in the first place.
The current state of enterprise tech stacks
At the heart of any enterprise lies its data — the core element that drives decisions and operations, and the thing this entire tech stack is here to protect. Traditionally, layers upon layers of technology have been added to govern and deliver this vital data. But each added layer, while enabling security and accessibility, also contributes to a ballooning complexity that negatively affects user experience and hampers operational efficiency.
Historically, such a multi-layered approach was deemed necessary for engineering a robust tech stack — and was the best possible approach given technologies available at the time. But with an Enterprise Browser, IT leaders now have the opportunity to build a tech stack that’s considerably leaner and much more effective.
Understanding the “Why” behind collapsing the tech stack
There are three business-critical reasons IT leaders should prioritize slimming the stack:
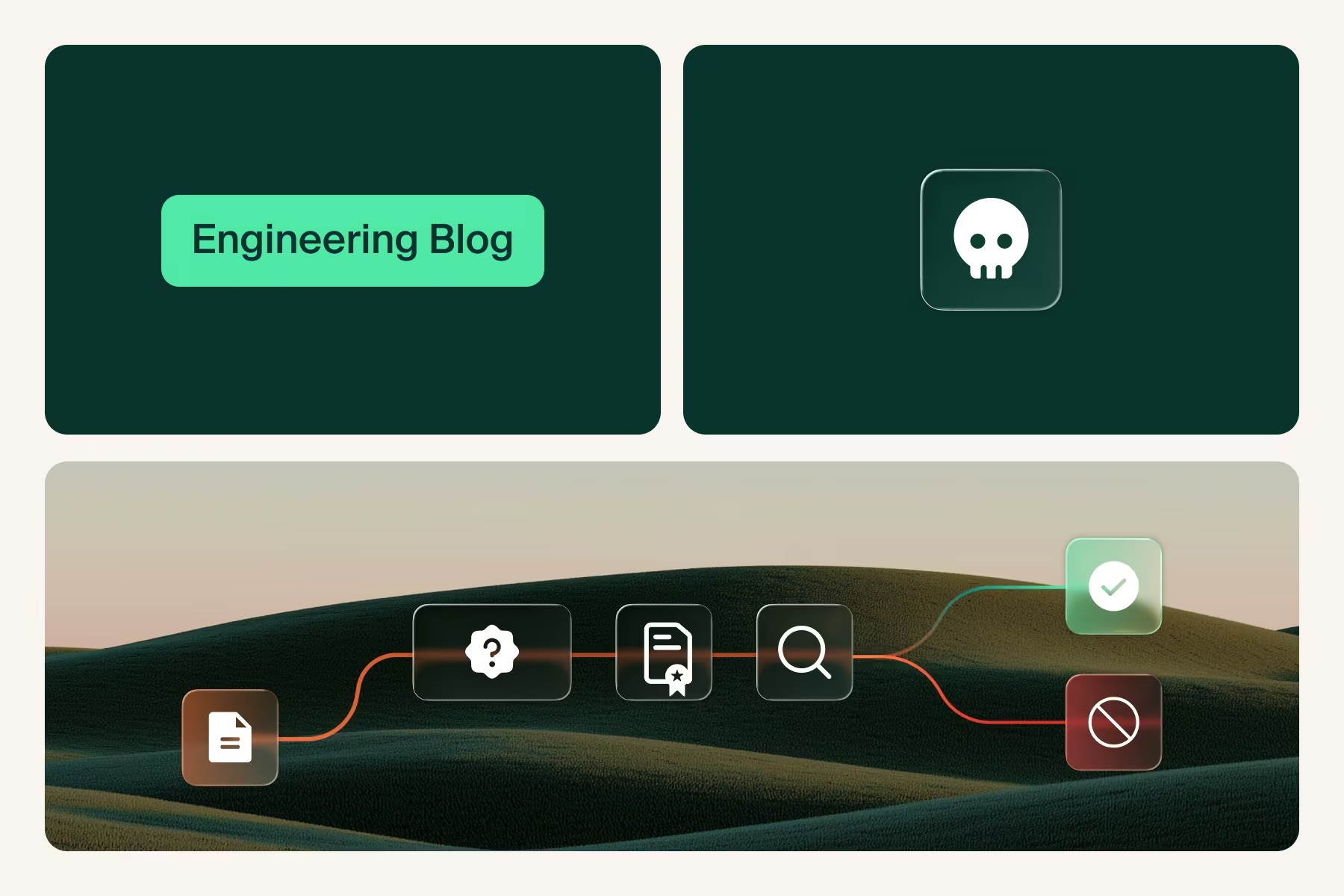
1. Protecting what matters: your apps and data. Complex tech stacks can create security blind spots. With numerous software solutions, each with its own security protocols and potential vulnerabilities, managing the risks associated with multiple attack vectors becomes daunting. By collapsing your tech stack, you reduce the number of potential entry points for cyber threats, reduce the overall attack surface, and simplify management.
2. Improving UX & boosting productivity — for IT and users alike. Each new tool in your stack demands time for onboarding, training, maintenance, and endless updating and patching. Further, these tools often do not interoperate well together, so time is spent troubleshooting the compatibility of the stack, wasting valuable IT resources. A streamlined stack means your IT workforce spends less time troubleshooting unnecessary agents and more time on productive work. General work is improved as well with end users no longer waiting for multiple agents to be installed, updated, and ready to impede their daily work.
3. Reducing significant IT spend. As costs grow every year — and new solutions render traditional ones obsolete — it’s important to look for opportunities to prune and optimize. For example, Virtual Desktop Infrastructure (VDI) and Desktop-as-a-Service (DaaS) are high-cost tools with diminishing value in a SaaS-first world. All the various agent-based technologies deployed at the endpoint represent an opportunity for simplification and cost reduction. If we consider DLP agents, CASB agents, EDR/XDR agents, SASE/ZTNA network routing agents, etc., the notion of collapsing the stack to a single solution is extremely compelling.
Start with BYO and self-service IT
Bring-your-own (BYO) environments and self-service IT are, by definition, the least standardized segments of the tech stack. They involve a variety of devices and platforms, each with its own security and compatibility issues. This diversity, while offering flexibility and convenience, can also be the starting point for inefficiency and security vulnerabilities.
A critical component in the quest to condense the enterprise tech stack is the adoption of an Enterprise Browser, which is built specifically to meet the complex IT needs of modern businesses. By integrating robust security, productivity, and accessibility features directly within the browser, these solutions alleviate the need for multiple technology layers. This integration ensures secure and streamlined access to business-critical enterprise applications and data, regardless of the device used. And by leveraging the browser — a familiar technology to every user — as the delivery vehicle for access and security, the BYO enablement process is dramatically simplified.
An Enterprise Browser also offers enhanced last-mile control over user activities and data flow, enabling enterprises to enforce policies consistently across all user endpoints. This shift towards a singular, centralized point for both access and security within the browser itself significantly simplifies the tech stack, making it more manageable and efficient, while bolstering the overall security posture of the organization.
Streamlining your BYO stack by implementing an Enterprise Browser can quickly help you prove the business impact of a leaner architecture. Even if you still have a few thick or legacy apps in play, those can be delivered within the Enterprise Browser, neatly in their own tab, with full security controls and audit capabilities. This massively reduces the infrastructure, carbon footprint, and cost required to host and deliver an always-on VDI-based desktop experience.
Simplification
Identifying redundant applications and services, and recognizing software that may not be compatible across all devices, can help reduce your number of managed devices — and the need to prep and ship those devices.
An Enterprise Browser simplifies all of this down to the nth degree. End users simply install the browser and get to work.
Security
Zero-trust is the security framework of choice for modern businesses, especially when it comes to BYO. Traditionally, this required adding endpoint agents, web portals, and VPNs to your stack to compensate for the consumer browser’s lack of security.
Security is embedded within the natural workflows of an Enterprise Browser, so end users can access and interact with applications and documents while sensitive data is protected. IT teams can define device security requirements (like disk encryption or OS patching) and require that BYOD devices meet these requirements before accessing enterprise applications.
Cost and time efficiency
Slimming your BYO tech stack with an Enterprise Browser significantly cuts down on a number of IT challenges with serious business impact:
- Licensing costs
- Help desk calls
- Time to onboard new employees and contractors
- Downtime lost to struggling with troubleshooting complex systems
Improved end user experience
With fewer layers of security and delivery to contend with, users no longer have to wade through multiple logins or wait for network-layer security checks. User frustration and IT ticket submissions are reduced as well.
“By 2030, enterprise browsers will be the core platform for delivering workforce productivity and security software on managed and unmanaged devices for a seamless hybrid work experience.”
Gartner, Emerging Tech: Security — The Future of Enterprise Browsers, Dan Ayoub, Evgeny Mirolyubov, Max Taggett, Dave Messett, 14 April 2023
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.
Evaluating the stack: what stays, what goes
The transition to a leaner BYOD stack requires a thorough evaluation of the existing tech stack. Here are some important things to consider as you embark on this process.
Assess the need for each layer
Start by evaluating the tools and platforms in use. Are there redundant applications serving similar purposes? Are there tools with very few active users? Consolidation can often lead to significant cost savings and efficiency gains.
Gather feedback on user experience and productivity
Your end users can offer invaluable insights on this front. Are they frustrated with a certain tool? Are key parts of their job getting slowed down because of a certain security requirement? Gather feedback to understand what works, what doesn’t, and where users face the most challenges.
Prioritize security
Evaluate each tool in your BYOD stack from a security perspective. How do they comply with your security policies? Are there gaps that need addressing, or tools that pose more risk than benefit? Are there other more secure alternatives that could displace or replace the current ones?
Focus on mobile integration
In a BYOD program, it's vital to evaluate how Mobile Device Management (MDM) and related securities can be streamlined or replaced. Look for solutions that offer a more integrated approach to securing mobile access to enterprise resources.
Perform a cost-benefit analysis
Review the costs associated with each component of your BYOD stack, including licenses, hardware, and maintenance. For each tool, weigh the costs against the benefits it provides. This goes beyond just the financial aspect to include factors like time savings, user satisfaction, and contribution to overall goals.
Embracing consolidation one step at a time
Collapsing your tech stack is more than a one-time project; it’s an ongoing process of adaptation and refinement. It requires a forward-thinking mindset, an understanding of your organizational goals, and a willingness to embrace change for better efficiency, security, and user experience.
Remember, the goal is not just to reduce the number of tools but to create an environment where technology empowers rather than hinders. With a thoughtful approach to collapsing your tech stack, you can build a more agile, secure, and productive organization.
.svg)


.svg)
.svg)
