The Enterprise Browser Blog

8
min read
|
Apr 7, 2026
How Island Enables CIPA Compliance
Secure browsing

8
min read
|
Mar 24, 2026
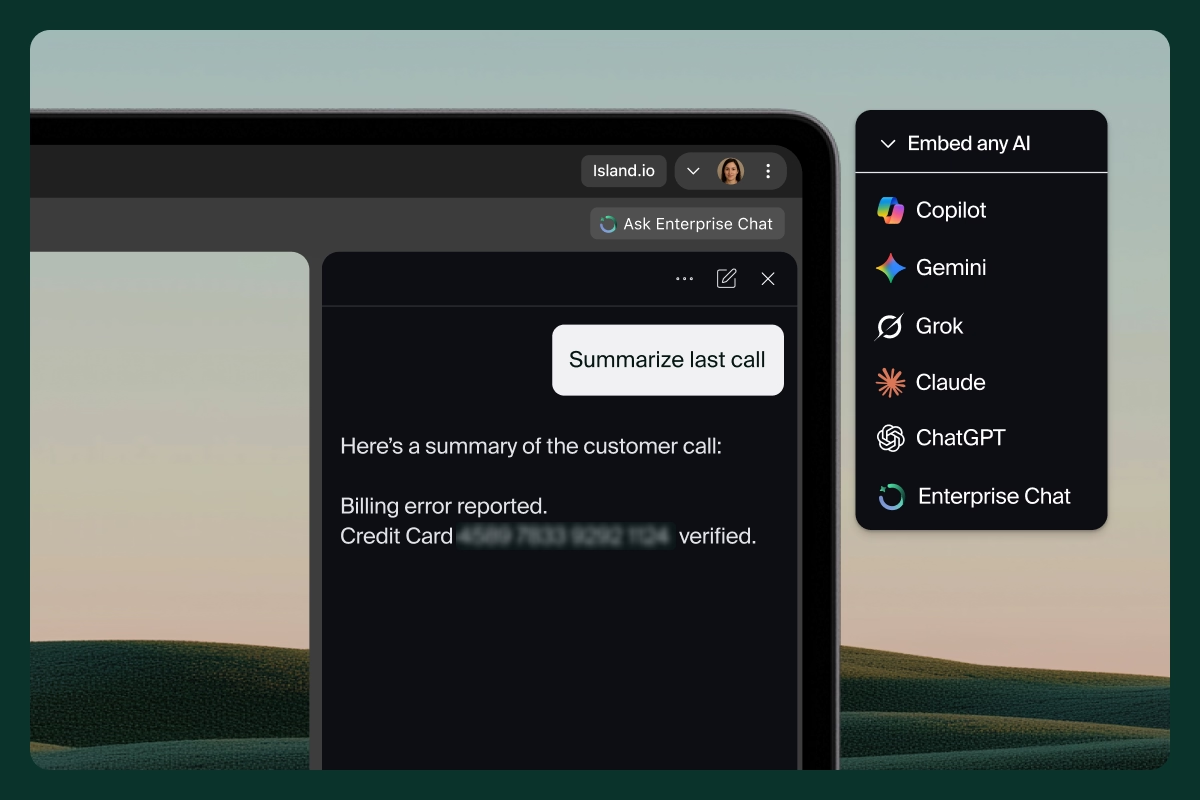
Island Enterprise AI Protect: Visibility, Control & Security
Artificial Intelligence/ AI
4
min read
|
Mar 17, 2026
Introducing Island AI Services
Artificial Intelligence/ AI
.png)
5
min read
|
Feb 26, 2026
Secure AI and Safe Browsing with Island and AWS Security Hub Extended
Enterprise security
7
min read
|
Jan 12, 2026
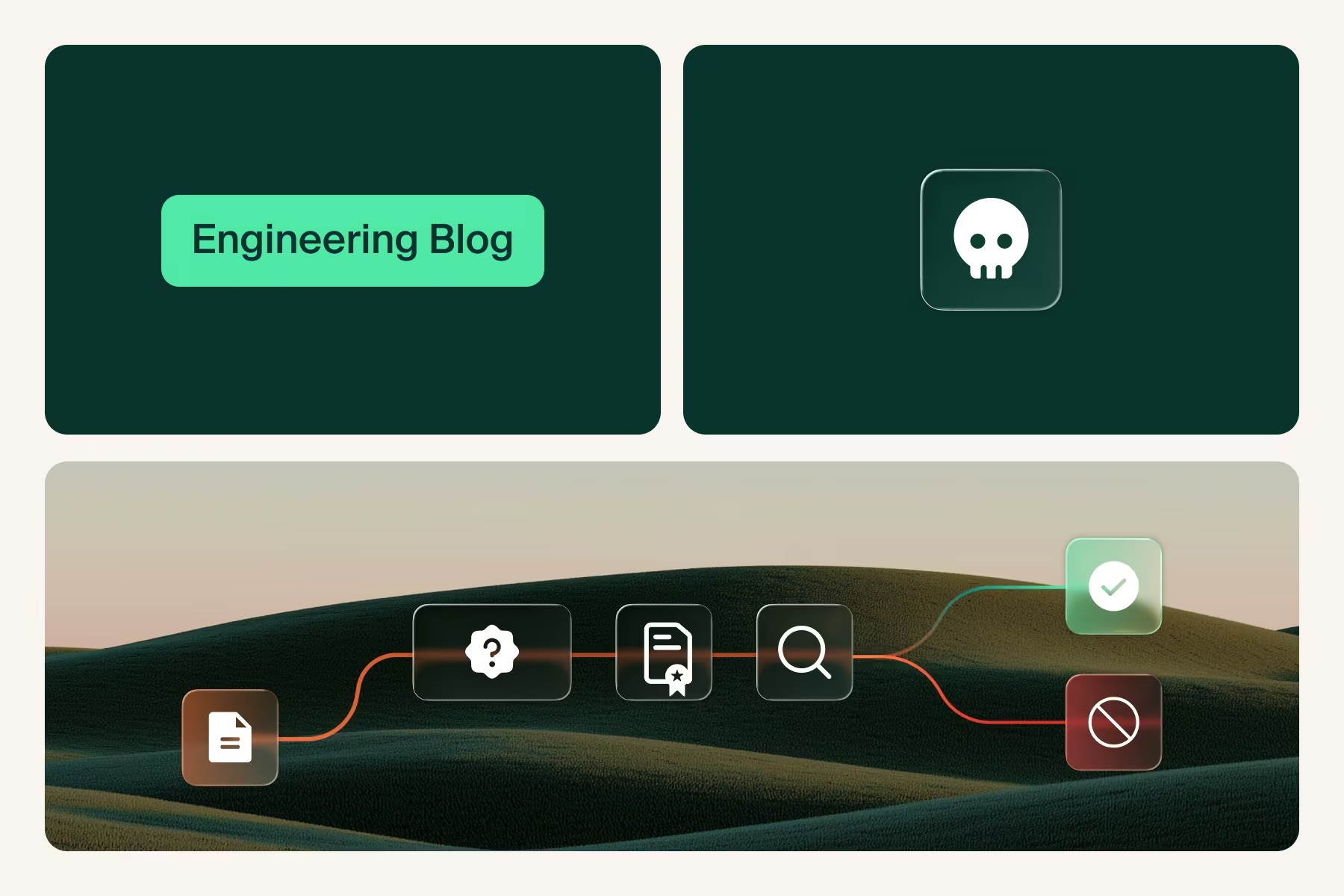
What It Really Means to Move Left of ATO
IT modernization








.svg)
.svg)
