Living up to the Hype: Gartner adds Enterprise Browsers to the latest Hype Cycle for Zero Trust Networking
The Enterprise Browser category is growing in importance as more organizations adopt a browser that’s built for enterprise work and delivers essential security controls and governance

Two massive shifts forever changed the enterprise workplace: Applications moved off the desktop to the cloud, and workers left the office to work remotely.
Together, these changes pushed IT and Security teams to rethink their strategy for delivering and securing enterprise workflows and data. Along the way, the web browser moved from a supporting tool for accessing information to the central workspace where most users do most of their work. It follows that the Enterprise Browser category is growing in importance as more organizations adopt a browser that’s built for enterprise work and delivers essential security controls and governance.
The most recent GartnerⓇ Hype Cycle(TM) for Zero Trust Networking named Island as an Example Vendor for Enterprise Browsers. In the report, they highlight several of the key drivers for customer adoption, including “providing Day 1 access for new organizations gained through mergers and acquisitions, contractor access management, or as layered security controls on top of fragile critical infrastructure.”1
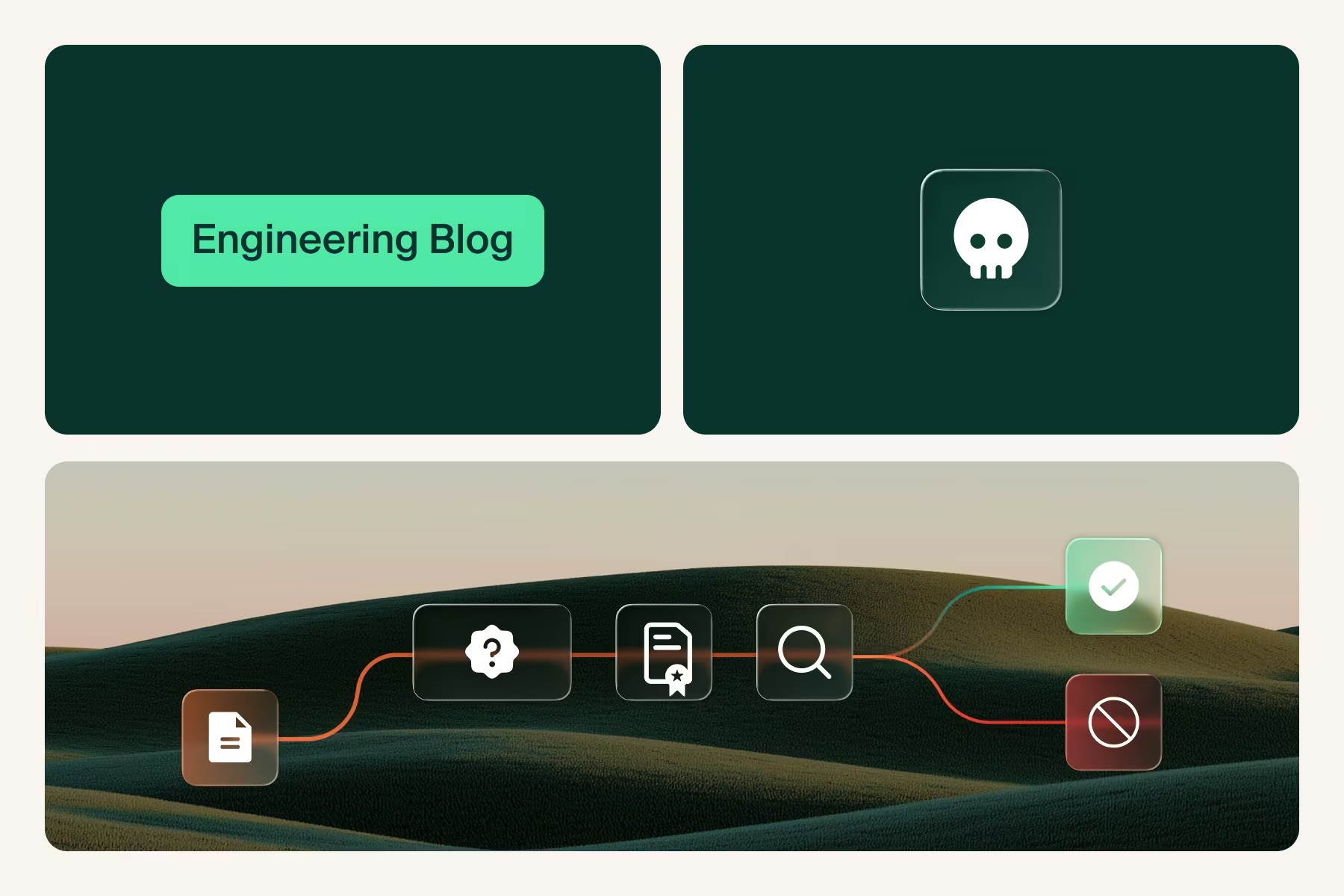
In the context of a zero trust security framework, the Island Enterprise Browser offers a welcome alternative to infrastructure-heavy legacy security solutions. The browser holds a privileged location within the application workflow: it knows the user’s identity, the posture of the device it’s running on, the network it’s connected to, the geographic location it’s operating in. This creates the foundation for zero trust access policies, even for deployments that challenge legacy security solutions. As the report identifies, “Existing security solutions often struggle to support unmanaged devices. This is an area where enterprise browsers have found early traction in the market, by providing an acceptable level of secure remote access that is able to maintain a mostly familiar end-user experience.”1
Where the Enterprise Browser stands apart is its ability to extend zero trust principles inside an application. With full visibility and control of the specific actions and data, the Enterprise Browser can apply the least-privilege principles within any application. For example, a call center employee could view a customer record in their CRM with certain sensitive fields redacted and be restricted from printing, saving, or exporting that information. Or a contractor could gain access to an internal system in read-only mode for a limited period of time. In these there’s no dependency on the application itself to support role based access policies or redactions, as it’s done within the Enterprise Browser itself.
The Enterprise Browser represents a new approach to security that puts access controls, data protections, and application visibility at the point of maximum impact: inside the browser. To learn more about how the Enterprise Browser creates new opportunities for IT, Security, and the enterprise workforce more broadly, read a recent research report from GartnerⓇ about the Future of Enterprise Browsers 2.
1 Source: Gartner, Hype Cycle for Zero Trust Networking, Andrew Lerner, John Watts, Dan Ayoub, et al., 18 July 2023
2 Gartner, Emerging Tech: Security — The Future of Enterprise Browsers, Dan Ayoub, Evgeny Mirolyubov, Max Taggett, Dave Messett, 14 April 2023
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, express or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally, and HYPE CYCLE is a registered trademark of Gartner, Inc. and/or its affiliates and are used herein with permission. All rights reserved.
.svg)


.svg)
.svg)
