Navigating the Challenges of Contractor and Third-Party Access

It’s been impossible to miss the recent cybersecurity incidents involving contractors and third-party access to organizational resources. While these headlines are hardly new, their impact is now exponentially more serious given the major shift to hybrid work, paired with mixed cloud and on-premises hybrid architectures.
Contractors and third parties often serve as the functional backbone of many operations. In some cases, they are individuals performing a specific function. In others, it’s a third-party organization performing an entire function like logistics management or HR. To ensure at least a basic level of security, organizations typically ask them to legally attest to their understanding of their responsibilities toward protecting the critical resources they are given access to. This may also involve rigorous inspection of the contractor’s controls and resources. But given the urgency of many contractors’ work, these inspections are often treated as a mere “checkbox.” Regardless of the need for speed or not, it’s a given that onboarding contractors and third parties is slow, expensive and cumbersome. Here’s why.
Third parties need to be granted access to an organization’s critical systems just to do their jobs, which organizations typically do using one of these two approaches;.
- They allow third parties to use their own devices
- They ship a company-owned device that the contractor or third party must use to access these systems and fulfill their duties
Both approaches involve different complexities and levels of risk that cause unnecessary pain on both sides. Let’s take a closer look:
Unmanaged Contractor and Third-Party Devices
As uncovered in recent news stories, third parties very often use their own devices. The advantages of this approach are fairly obvious. Allowing these resources to use personal devices saves time, reduces onboarding costs and allows the third-party’s resources to operate in a familiar environment, which significantly speeds up productivity.
But this approach has its downsides as well. It requires giving individuals account credentials to the systems (VPNs, Virtual Desktops, and actual applications) they need to perform their roles. Onboarding this kind of access is complex, costly, and requires ongoing attention to manage provisioning and revoking access and credentials.
Managed Devices for Contractors or Third-Party Access
On the other hand, many organizations opt to ship a company-owned, managed and pre-configured device to the contractor or third party. The upfront cost and effort involved in buying, building, and shipping these devices at scale is immense. Not to mention the timing - it can take a month or longer to get a single contractor up and running. It also creates a steep learning curve on the third-party’s side to integrate new devices and systems into their workflow. While ultimately this may be the less risky approach, the significant tradeoffs feel unacceptable to both the organization and the third party.
The Ongoing Effort
In both of the above scenarios, provisioning alone is a serious organizational challenge. And yet, it’s only the beginning. Ongoing governance is also necessary to ensure contractor and third-party access is limited to only the sources and systems necessary to perform the responsibilities they were hired to carry out. This requires uncomfortable architectural choices to be made to balance the often opposing forces of efficiency and risk. On a practical level, these considerations include whether to use VPN backhaul, cloud forward/reverse proxy implementations, virtual desktops, CASB, DLP, Web Gateways, or ZTNA technologies to govern third-parties safely. Unfortunately, these decisions cause complexity and costs to explode, leaving the organization vulnerable to the contractor or third-party risk. This was made quite evident in recent headlines where the level of complexity for offshore third-party access was undoubtedly one of the core issues.
The Enterprise Browser: An Ideal Way to Onboard and Oversee Contractors
We’ve always been forced to choose between security and complexity or speed and efficiency. This is what we challenged ourselves with. A way to ensure security while enabling work. Maximum efficiency, minimum risk. And out of this challenge came the industry’s first browser built for the enterprise. Imagine, instead of all the organizational challenges, all the workers’ frustrations, all the costs and complexities, contractors or third parties just logged into a browser that had all the resources they needed waiting for them. This is what the Enterprise Browser can do for work.
Let’s start with provisioning. For third-party organizations or contractors using their own devices, you provide a download link for the Island installer. Once the browser is installed (it takes less than a minute), you give them credentials and access privileges aligned with their role, and in seconds they begin working. The applications they need are immediately made available with no complex configurations or additional software required. And for organizations choosing to provide their own managed devices to contractors or third parties, simply include the Island Enterprise Browser in your device build, and the process is exactly the same as above.
Once the user is working on the Island Enterprise Browser, your organization’s applications and associated data are fundamentally protected. Island’s unique last mile controls allow you to easily create policies to govern application and data access. And further, it allows you to control who has privileges to add new users, who is authorized to change or copy data, and whether or not a user can download, screenshot or save content.
You also get extraordinary visibility in a way that simply wasn’t possible before; deep forensic audit logging to keep a close watch on what these resources are doing as they do their jobs. You can even output these activities in real-time to data aggregation environments such as SIEM to monitor user behaviors and actions to quickly discover unwanted activities. Island sheds light on a unique dimension of user-based data by keeping tabs on the contractor or third-party’s actions within the browser window.
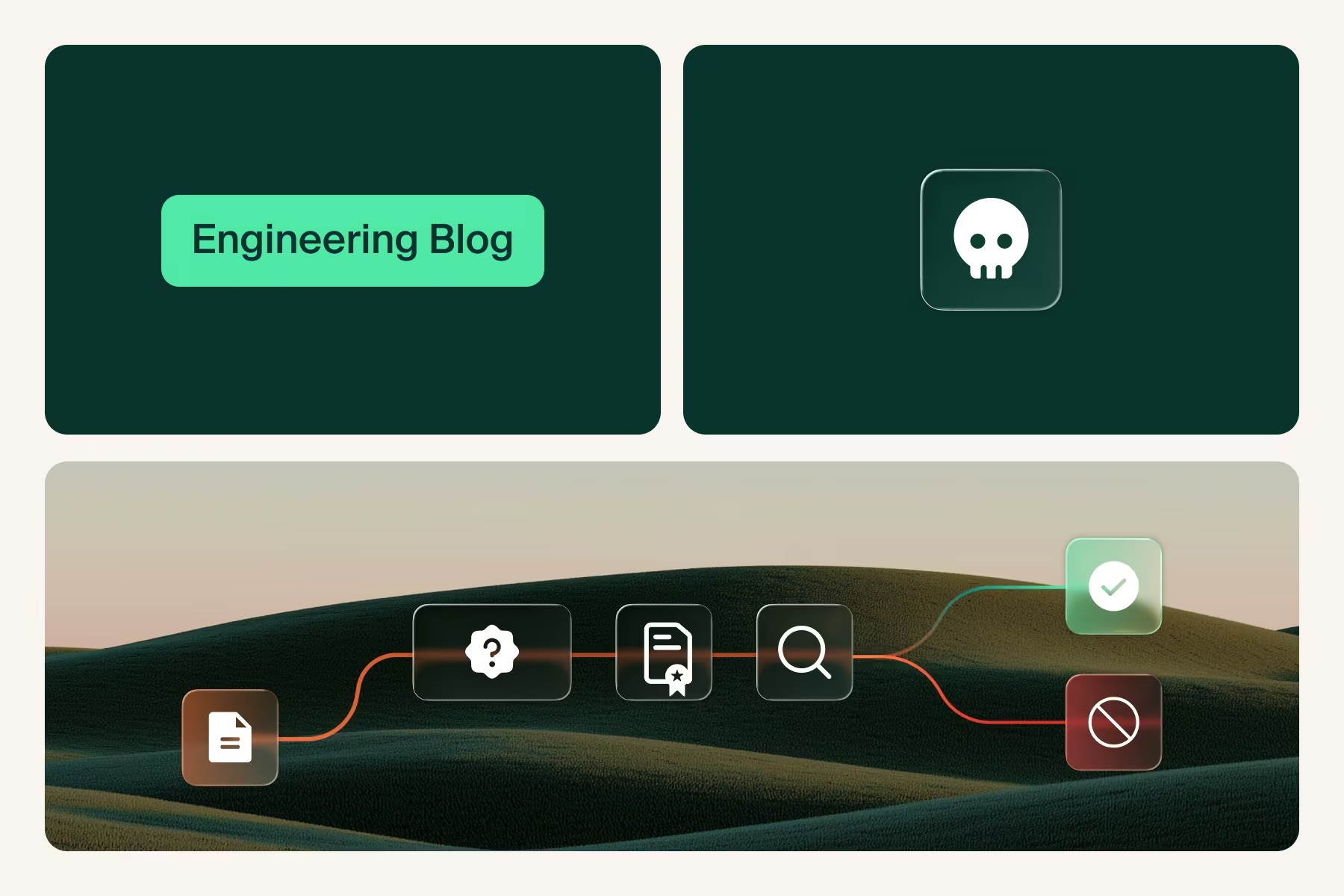
As seen in recent news stories, the inability to govern contractor or third-party usage of key application areas was what allowed attackers to manipulate backend application areas that very well could have been out of the scope of the third-party’s work in the first place. Last-mile control and deep logging could have been the difference between identifying and preventing any sort of compromise and hunting down and remediating the problem once the damage is done.
And while it’s essential to govern the actual contractors or third parties as they engage in critical application areas, it is equally necessary to ensure that they are protected from outsiders who might leverage them as a vulnerable attack vector in the organization. Island ensures that the browser is safeguarding the entire journey on all sides, at all times. Island delivers several key capabilities to ensure that attackers are thwarted in their attempts to use the contractor or third party as a vector of compromise. These capabilities include:
- Man-in-the-Middle Protection
- Anti-tampering Protection
- Browser Isolation
- Malware InspectionDocument Isolation and Disarmament
- Malicious and Unknown Site Categorization
These built-in capabilities ensure that the organization’s applications and the contractor or third party are always protected from attack as they perform their work.
The Bottom Line.
Third-party contractors and resources are pervasive and the practice is growing exponentially as the gig economy and the need for hyper specialized project work expands. Companies are purposefully building this practice into their business models, making these services very often mission critical to operations. But recent compromises using this vulnerable channel threaten to either reduce the practice entirely or forcefully add more cost, complexity and inefficiency into the process.
It is time to consider a whole new way to approach contractors and third-party access. We need to be able to get people to work quickly, and allow the organizations and people on both sides of the equation to be confident that both the applications, data and users are protected. With Island’s Enterprise Browser at the core of these use-cases, you can safely and quickly get people to work, create a great user experience and be confident your data and applications are protected.
.svg)



.svg)
.svg)
