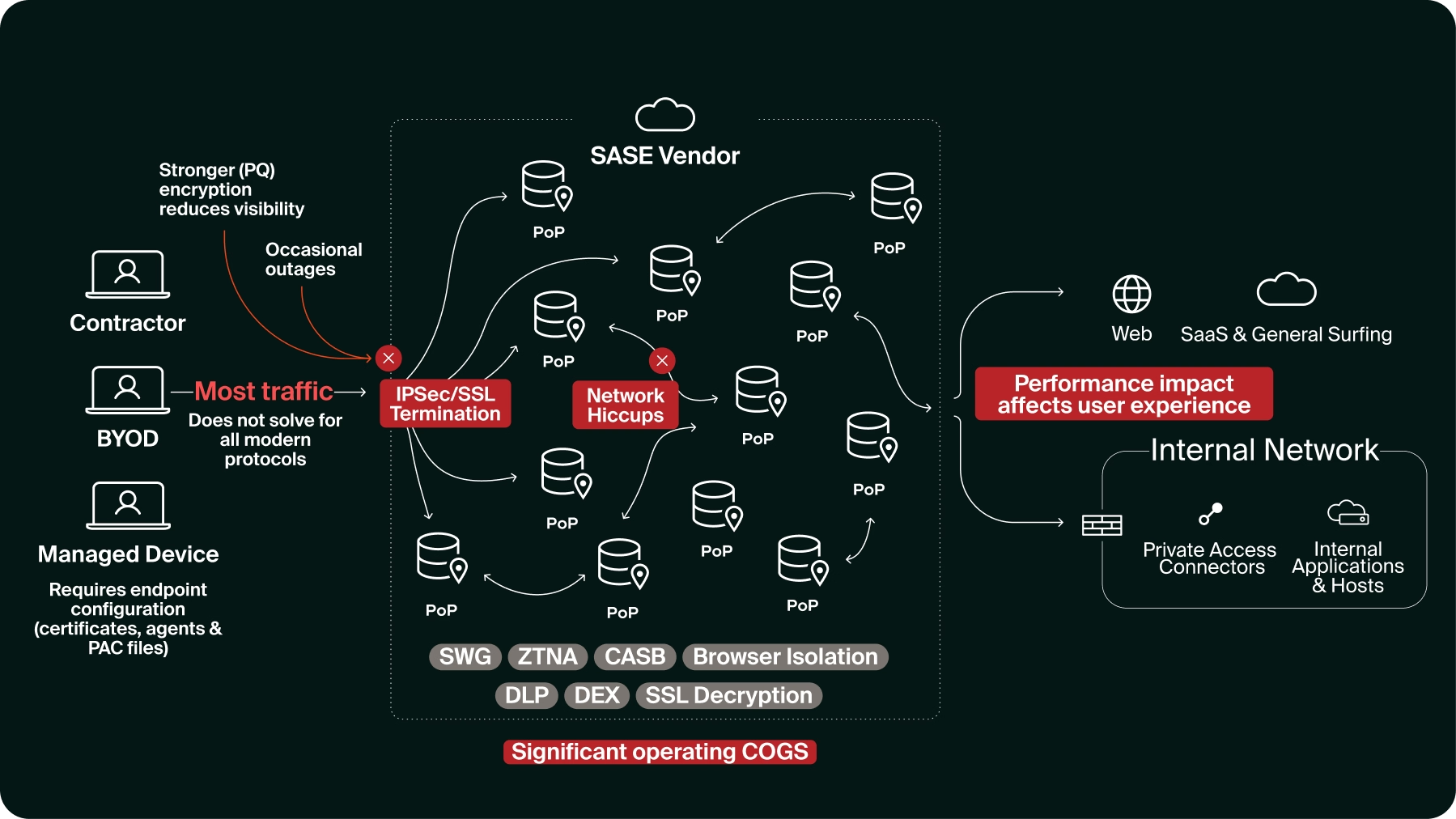
Why SASE Backhauling Falls Short for Modern Work
SASE optimized enforcement around distant PoPs and traffic inspection. Modern work happens at the interaction layer. Here’s why enforcement must move to the last mile.

SASE architecture was a generational step forward, a solution that was born of necessity. When organizations moved to the cloud and workforces dispersed globally, the traditional perimeter security collapsed. The answer was to converge networking and security into a cloud-delivered architecture that could scale with hybrid work and digital transformation. By routing sessions through globally distributed Points of Presence (PoPs), SASE promised unified policy, consistent enforcement, and secure access regardless of location.
It worked for that era. But work didn’t stop evolving.
Users aren’t waiting for packets to route through cloud proxies anymore. A contractor copies customer data from Salesforce, pastes it into ChatGPT for analysis, then downloads the output to share with partners. An employee uploads an internal pricing spreadsheet to their personal Dropbox. A third-party consultant accesses your SaaS stack from an unmanaged laptop IT will never touch.
But before any of that work even happens, traffic is backhauled through distant inspection points. Sessions are decrypted and re-encrypted. Users feel it as latency. IT feels it as tickets, tuning, and constant policy adjustments. Security teams feel it as an expansion of bypass lists and inspection gaps. And inspection is becoming harder to sustain as modern encryption approaches post-quantum standards, limiting what proxies can reliably break and inspect.
Even after all that, the most important context is still missing. These actions don’t originate in the network. They originate at the moment of interaction, inside the application, at the presentation layer. The network only sees the session once traffic leaves the device. It does not see the copy event, the tenant context, the prompt intent, or where the output goes next. So the model creates friction and blind spots at the same time.
That architectural gap is the distance between where work actually happens and where enforcement is applied.
The world moved on, but the architecture didn’t keep pace
Fast forward to today, organizations have widely adopted SaaS, hybrid work has become the norm, and AI is deeply embedded in daily workflows. SaaS applications and cloud-native tools now define where business happens, not just where traffic flows.
Yet the predominant SASE execution model still relies on routing sessions through centralized Points of Presence (PoPs) for inspection and enforcement. The result is familiar to any IT or security leader: the architecture that was supposed to simplify operations becomes itself a source of friction.
Performance degradation that users feel daily
When every session routes through cloud PoPs for inspection and TLS decryption, regardless of whether direct access is available, latency is inevitable and becomes the baseline. In bandwidth-constrained geographies such as Brazil, Australia, or parts of the Middle East, it can render SaaS workflows inconsistent or borderline unusable. Real-time collaboration degrades under load, and users eventually seek workarounds just to stay productive.
Reliability concentrated into shared chokepoints
Security enforcement and decryption are concentrated in shared PoPs and centralized control planes. When inspection, decryption, and policy evaluation are concentrated in a small number of PoPs, resilience becomes fragile. A user in Toronto connected through a Detroit PoP may suddenly be rerouted through Chicago or New York during a failover event. Traffic shifts en masse, latency spikes, and active sessions reset. Certificate validation errors or control-plane updates can impact thousands of users at once. Failure is no longer local. It becomes systemic.
Operational complexity that compounds over time
Multiple service chains and overlapping policies across SWG, CASB, and ZTNA create troubleshooting nightmares. Rollouts stretch from weeks to months, environments evolve faster than deployment, and exception lists grow. As certificate pinning and modern app behaviors resist TLS inspection, teams are forced into ongoing exclusions just to keep critical apps running, expanding blind spots along the way.
Visibility gaps where it matters most
Network inspection shows destinations, connections, and decrypted payloads, but not user intent inside applications. It may see a file upload, yet miss what was copied into an AI prompt, web form, or moved between SaaS tenants. Persistent connections like WebSockets, common in modern SaaS and AI tools, can also become unstable when forced through proxy inspection, adding more friction without improving visibility.
Encryption as an accelerating constraint
As TLS encryption strengthens, moving towards post-quantum implementations, proxy-based ‘break and inspect’ becomes harder to sustain (and in some cases, impossible). Certificate pinning, mutual TLS, and application-specific encryption schemes force administrators to maintain extensive bypass lists, creating blind spots.
The result is a system optimized for controlling traffic, not for governing work. And as AI embeds itself into daily workflows, that gap becomes even more impossible to ignore.
AI didn’t break SASE; it simply exposed the architectural gap
AI didn’t create the problem. It just made the problem unavoidable. Modern AI workflows are not linear; they involve agentic, app-to-app communications that bypass traditional network inspection entirely. By the time an AI interaction hits the network, the 'moment of intent' has already passed. To govern AI, enforcement must live where the interaction begins. Users paste internal information into prompts, upload documents for analysis, use generated output, and move it downstream into reports, code repositories, and customer communications. Agentic workflows orchestrate tool-to-tool interactions that don't resemble traditional network traffic at all, happening at machine speed and entirely within the application context.
Network proxies can see the connection to an AI service. They can sometimes break and inspect prompt content after it leaves the device. But they cannot reliably interpret intent, understand in-application actions, or track how generated output moves through subsequent workflows. The visibility required to govern AI effectively simply doesn't exist at the network layer. It exists at the point of interaction.
Traditional SASE vendors respond the only way their architecture allows: binary enforcement. Allow access or block it. The result is that organizations either ban AI use (thereby increasing shadow IT) or accept uncontrolled risk. Neither outcome is scalable for modern distributed teams that rely on AI for innovation and productivity.
The limitation isn't a feature gap. It's an architectural mismatch between where enforcement lives and where work actually happens.
Traditional SASE’s struggle with contractors and unmanaged devices
Another emerging reality is the proliferation of contractors, partners, and BYOD endpoints.
Contractors and partners often operate outside managed environments. They access enterprise systems from devices IT will never control, outside standardized posture or agent enforcement. That reality stretches network-centric enforcement models to their limits.
Traditional SASE frameworks expect managed endpoints and centralized inspection to function reliably. But unmanaged devices complicate posture assessments and often evade consistent enforcement unless organizations introduce heavyweight agents or intrusive network tunneling.
Security leaders face a hard choice: lock down access aggressively, slowing or blocking contractors, or loosen policies and expose risk. Neither outcome scales modern distributed teams or enterprise organizations.
This friction directly impacts productivity and collaboration, the very things organizations need to thrive and security was meant to protect.
The (not so) subtle cost that doesn’t align with value
Beyond technical limitations, proxy-centric SASE creates a cost structure that security and finance leaders recognize immediately: upfront investment doesn't translate to proportional value.
Licenses are purchased at scale. Deployments take months. Coverage remains partial. Features are enabled but never fully tuned. Many enterprises find themselves running fragmented SASE stacks or partially activated capabilities, with multiple consoles and policy engines operating in parallel.
Enforcement looks complete on dashboards while gaps persist in practice. IT teams spend cycles troubleshooting policy conflicts, managing certificate exceptions, and explaining to users why sanctioned applications perform worse than personal ones.
SASE’s ambition was to unify network and security functions into a single framework.
The challenge now is that unification alone does not align enforcement with where the modern enterprise actually engages with data and where work is performed.
This isn't a vendor-specific problem. It's a structural consequence of architectures that require mandatory traffic backhauling, SSL break-and-inspect dependencies, and centralized enforcement through distant inspection points. The operational overhead compounds faster than the security value accumulates.
What modern enterprises actually need
Modern SASE doesn’t start by asking how to route traffic.
It starts by asking where work actually happens.
Enforcement has to move closer to the interaction layer, where identity, context, and intent are clearest. The cloud still matters. The network still matters. But they shouldn’t be the first place where policy is executed. They should support it.
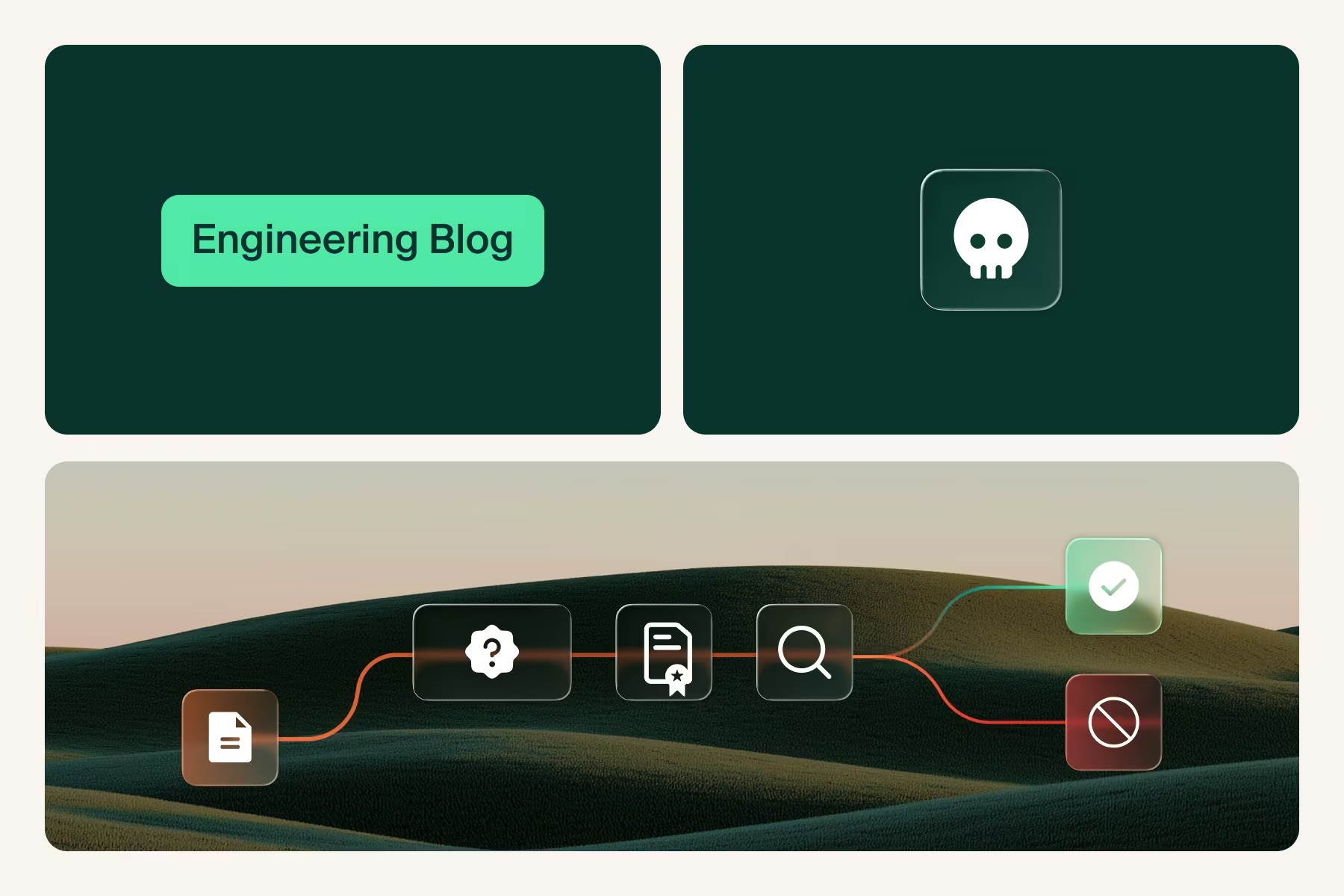
That shift requires three structural changes:
- Policy execution at the last mile
Identity, device posture, network and geolocation, application context, and session state are evaluated at the moment of interaction, before data leaves the device, rather than after traffic enters a distant inspection path. This is what true Zero Trust enforcement looks like in practice. It removes latency, improves reliability, and provides visibility into user actions that network flows simply cannot capture.
- Selective use of cloud services
Global networks provide resilience, failover, and centralized visibility. But they should support the architecture, not define it. Traffic should be steered into cloud inspection only when deeper analysis or routing support adds value.
Not every session deserves the same treatment. Modern architectures must evaluate each interaction and decide in real time: go direct, inspect selectively, or block. Uniform routing is simple to implement, but it is not aligned with how work actually happens.
Backhaul becomes the fallback, not the default.
- Unified policy fabric across enforcement points
Browser controls, endpoint governance, network services, and SaaS API protection operate under one policy engine with one audit trail. No service chaining. No policy re-evaluation at different PoPs. Policy is defined once and enforced consistently wherever it is executed.
In this model, security doesn’t slow work. It enables it. Applications go direct. Enforcement happens once. AI governance becomes practical. And SASE finally aligns with how modern enterprises actually operate.
.png)
A unified environment for secure work
What enterprises truly need isn’t merely another phase of network evolution. They need a unified execution environment for secure work.
This environment:
- Treats the interaction layer (the Enterprise Browser and endpoint) as the first surface for policy evaluation and enforcement
- Extends enforcement to endpoints and thick clients when required, maintaining a consistent policy across the entire workspace
- Applies context, identity, and intent as policy inputs, making decisions with full visibility into who, what, where, and why
- Uses global network services selectively by steering traffic into cloud inspection only when deeper analysis or routing adds measurable value
When policy is evaluated at the point of work (in the browser, on the device), security gains the visibility and control that network-centric models fundamentally cannot provide. Users experience faster performance because most sessions go direct. IT teams operate simpler architectures because enforcement doesn't depend on mandatory backhauling. And organizations can govern AI, SaaS, and hybrid workflows with precision instead of binary allow-or-block decisions.
The result is so much more than just stronger security. It’s a seamless orchestration between access, security, governance, and productivity.
Bottom line
Traditional SASE was foundational in bringing network and security closer, and the evolution ahead isn’t about undoing that. It’s about aligning enforcement with how work happens today, through applications, at the endpoint, and at the moment of interaction.
That means moving enforcement to where it matters most: the point of work, not the point of transit.
When security meets work where it actually happens, friction dissolves. Productivity accelerates. Visibility and governance abound. And the promise of SASE, unified, consistent, scalable protection finally aligns with how modern enterprises actually operate.
See how Island enforces policy at the point of work. Request a demo.
.svg)

.svg)
.svg)
